Upgrading existing physical access control to comply with PIV mandates
24 January, 2012
category:
 By Dave Adams, Senior Product Marketing Manager, HID Global
By Dave Adams, Senior Product Marketing Manager, HID Global
Beginning in fiscal year 2012, U.S. government agencies must upgrade their physical and logical access control systems to provide federal employees and contractors with more secure and reliable forms of identification using Personal Identity Verification (PIV) credentials. These credentials must leverage smart card and biometric technology in accordance with National Institute of Standards and Technology guidelines embodied in FIPS 201. These upgrades must be completed before federal agencies may use development and technology refresh funds to complete other activities.
Until recently, upgrading to FIPS 201 standards was a difficult and expensive process that involved a number of suppliers and consultants. It also generally required a wholesale replacement of the current physical access control system (PACS) infrastructure, including head-end servers, panels and door control hardware.
This has all changed. With the advent of modular hardware solutions and turnkey implementation strategies, agencies can establish a clear migration path from existing credentials and preserve investments in their existing PACS infrastructure. This also allows them to support changing security requirements and enable cost-effective enhancements down the road.
Understanding FIPS 201 requirements
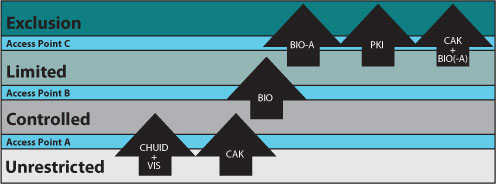
HSPD-12 set a clear goal to improve physical access control security and reliability through the use of government-wide standards. The FIPS 201 standard went further to define the specific characteristics of an interoperable identity credential to be used throughout government. Another important document, SP 800-116, introduced the concept of “Controlled, Limited, and Exclusion” areas, and required agencies to employ risk-based PIV authentication mechanisms for different areas within a facility (see Fig. 1).
Fig. 1: Innermost use of PIV authentication mechanisms
Simplifying the compliance process
Ideally, it should be possible to upgrade an existing PACS infrastructure so that it can authenticate credentials across the full range of assurance levels as defined in SP 800-116, without requiring a wholesale rip-and-replacement.
This is now possible using a modular hardware approach that delivers a high level of flexibility for future modifications. Agencies can install a combination of enhanced readers and FIPS 201 authentication modules that operate with existing components in the current PACS infrastructure. It is easy to deploy and eliminates the need to acquire a complicated mix of expertise, technologies and suppliers.
At the core of this solution is a reader that must feature EAL5+ Secure Element hardware. This ensures tamper-proof protection of keys and cryptographic operations. Additionally, the reader should use the industry-standard Open Supervised Device Protocol (OSDP) communications specification to establish a secure bidirectional link with FIPS 201 authentication modules.
To achieve compliance, agencies simply deploy the new readers and install authentication modules between the readers and the existing PACS panel. This upgraded access control system can now perform PIV authentication tasks across all PIV permission levels, with a validation server providing centralized control of assurance level settings and the distribution of validation data. This modular compliance system performs all necessary PIV authentication steps, beginning at the time of enrollment.
When a credential with the appropriate assurance level is presented to a corresponding reader, the authentication module validates the card according to the assurance level setting. The authentication module then extracts the FASC-N or UUID from the card and passes it on to the PACS panel for an access decision and logging. To prohibit access by revoked cards, the system retrieves and checks the card revocation status from the issuing certification authority or hotlist.
To validate visitor PIV cards, authentication modules use the Server-based Certificate Validation Protocol (SCVP) to establish a chain of trust through the Federal Bridge. Vendors must have first successfully completed cross-certification to the PIV-I standard via the CertiPath Bridge, which ensures interoperability across government agencies and with non-government members of the Federal Bridge. For invalid cards, the authentication module is configurable to send a preset badge ID to the PACS panel (for logging and investigation) and/or close an output relay (to trigger a video camera, for instance).
In the case of communications interruption in the validation process, authentication modules maintain an updated validation data cache that enables them to function “offline.” Meanwhile, strong authentication continues at the door.
Other features further improve simplicity and flexibility. By capturing cardholder data the first time a card is presented for validation to a reader connected to an authentication module, this data can be shared with other authentication modules. This feature delivers several benefits. It makes it possible to use existing access control enrollment functionality and it enables integration with an identity management or card management system. It also enables the use of third-party enrollment packages.
Meeting current and future compliance needs
Until recently, agencies faced with the mandate to upgrade their physical access control system to FIPS 201 compliance were required to work with multiple vendors and often had no choice but to replace their entire PACS infrastructure. The latest, modular solutions give agencies a single point of responsibility and accountability for achieving compliance without a wholesale rip-and-replace upgrade.
The solutions also provide the means to support many compliance needs, including PKI-at-the-door mandates as well as PIV-I and PIV-C requirements for cards issued by non-federal entities. For these and other challenging compliance requirements, today’s modular solutions give agencies a migration path that protects their current PACS investments while enabling them to employ risk-based security levels in selected areas, as required, and to leverage ongoing improvements in access control technology.




